DMARC Checker - Verify Your Domain’s Email Records
Check your DMARC record instantly with our free DMARC checker tool. Validate DMARC configuration, identify issues, and secure your email domain.
Trusted by Businesses Worldwide
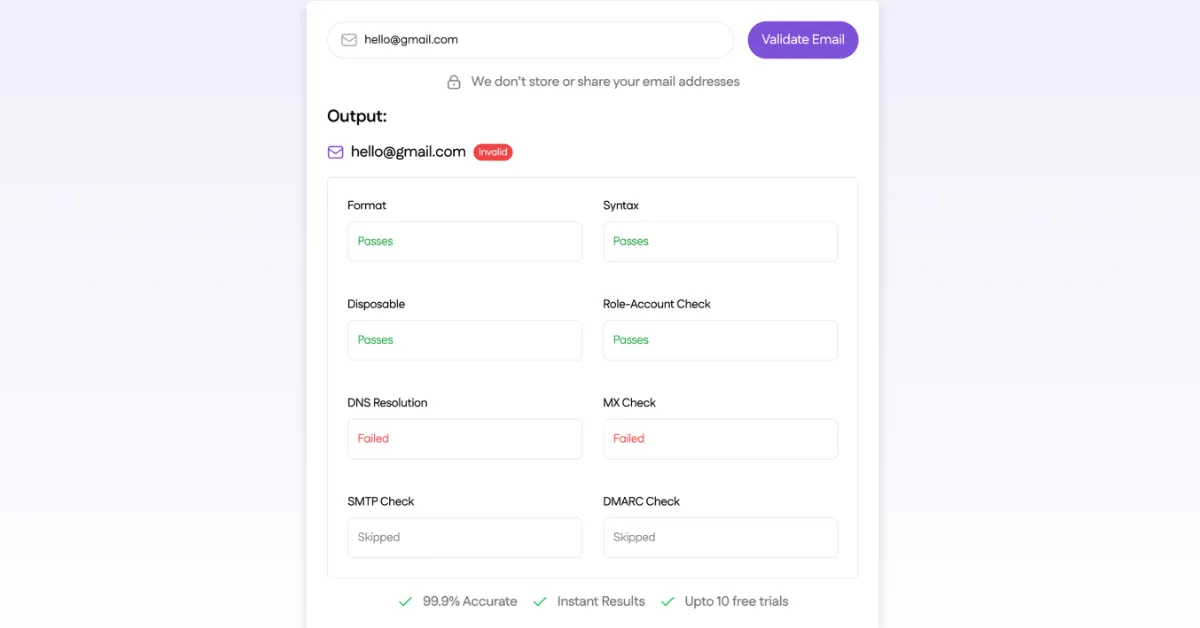
WHAT THIS DMARC CHECKER CHECKS
Our DMARC checker performs real-time DNS lookups to analyze your domain's email authentication configuration. Here's what it verifies when you run DMARC checks:
1. DMARC Record Presence
The first step in DMARC checking is confirming whether a DMARC record exists in your domain's DNS. Our tool queries the _dmarc subdomain (e.g., _dmarc.yourdomain.com) to detect if you've published a DMARC policy. If no record is found, your domain has no protection against email spoofing.
2. DMARC Policy Status
Our DMARC checker identifies your active policy setting and displays whether your domain is in:
- p=none (Monitoring Mode): Collects authentication data without blocking emails. Provides visibility but no active protection.
- p=quarantine (Filtering Mode): Sends suspicious emails to spam/junk folders. Offers moderate protection while legitimate emails still deliver.
- p=reject (Enforcement Mode): Blocks unauthorized emails completely. Maximum security against domain spoofing.
Understanding your policy status helps you determine whether your domain actively prevents email spoofing or simply monitors authentication activity.
3. SPF Alignment
SPF alignment checks whether the domain in the email's "From" header matches the domain authorized by your SPF record. Our DMARC record checker verifies if your SPF configuration supports DMARC authentication by confirming:
- SPF record exists and is valid
- Alignment mode is properly configured (relaxed or strict)
- The Return-Path domain aligns with your policy requirements
Misaligned SPF can cause legitimate emails to fail DMARC checks even when SPF passes.
4. DKIM Alignment
DKIM alignment verifies that the domain in the visible "From" address matches the domain in the DKIM signature. When you use our DMARC checker online, it confirms:
- DKIM signatures are properly configured
- The signing domain aligns with your DMARC policy
- Alignment mode (relaxed or strict) is correctly set
At least one of SPF or DKIM must align for DMARC to pass. Proper DKIM alignment is critical for email authentication.
5. Reporting Configuration (rua / ruf)
DMARC generates reports that show who's sending emails using your domain. Our DMARC checker verifies whether reporting is properly configured:
- rua (Aggregate Reports): Daily summaries of authentication results sent to specified email addresses. Essential for monitoring email authentication trends.
- ruf (Forensic Reports): Detailed failure reports for individual emails that fail authentication. Useful for investigating specific incidents.
Without proper reporting configuration, you won't receive visibility into authentication activity or potential threats.
6. Record Syntax Validation
DMARC records use specific syntax that must be formatted correctly. Our tool validates:
- Required tags are present (v=DMARC1, p=policy)
- Optional tags are properly formatted
- No syntax errors that could break authentication
- Tag values are within acceptable ranges
- Record doesn't exceed DNS character limits
Even minor syntax errors can render your DMARC record invalid, leaving your domain unprotected. Our DMARC checker identifies these issues instantly. Looking to go beyond DMARC monitoring? Protect your entire email infrastructure with real-time validation and authentication tools from SanitizeEmail.
WHAT DO THE DMARC RESULTS MEAN?
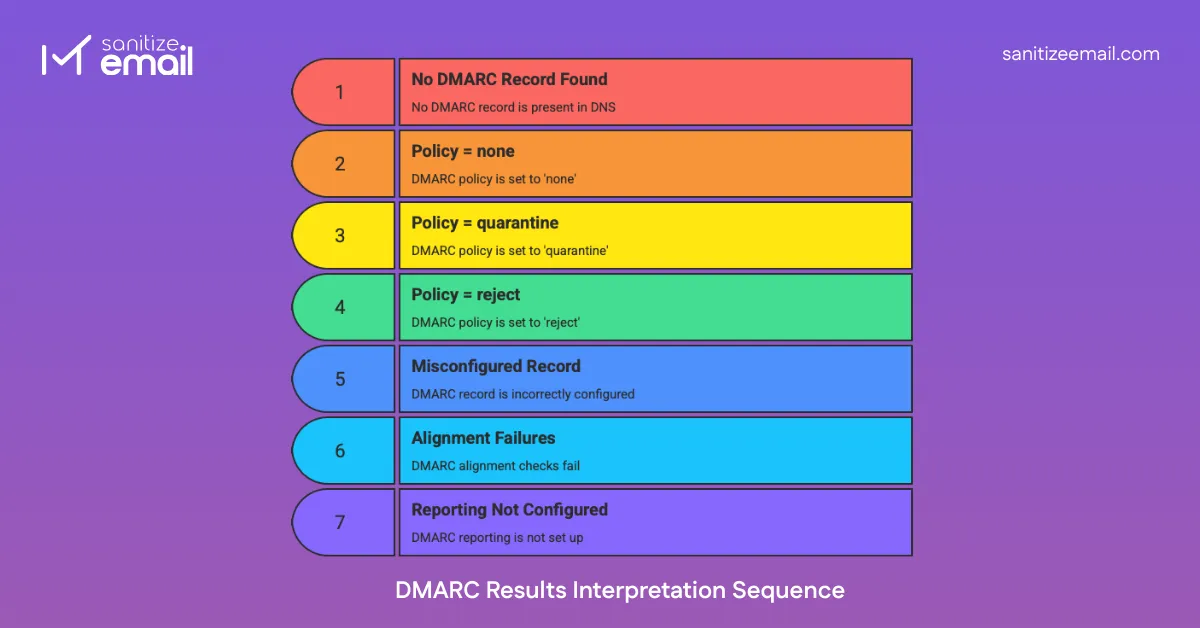
After running DMARC checks on your domain, you'll receive a result that shows your authentication status. Understanding these results helps you determine what action to take.
Step 1: Email is Sent: A sender attempts to deliver an email claiming to be from your domain. The email includes headers that identify the sending server and domain.
Step 2: SPF Check: The receiving mail server checks if the sending IP address is authorized to send emails for your domain by looking up your SPF record in DNS. This verifies the server is legitimate.
Step 3: DKIM Check: The server verifies the DKIM signature attached to the email. This cryptographic signature confirms the message hasn't been altered in transit and comes from an authorized source.
Step 4: Alignment Evaluation: DMARC checks if the domain in the visible "From" address aligns with the domains authenticated by SPF and DKIM. At least one must align for DMARC to pass.
Step 5: Policy Enforcement: Based on the authentication results and alignment, the receiving server applies your DMARC policy:
- If checks pass: Email is delivered normally
- If checks fail: Your policy determines whether the email is delivered, quarantined (sent to spam), or rejected entirely
Step 6: Reporting: The receiving server generates a DMARC report and sends it to the email addresses specified in your DMARC record (rua for aggregate reports, ruf for forensic reports). These reports show authentication results and help you identify legitimate senders and potential threats.
This process happens automatically for every email, providing continuous protection against domain spoofing without requiring manual intervention.
Common DMARC Errors
When running DMARC checks, you may encounter these common configuration problems. Understanding them helps you fix issues quickly and maintain proper email authentication.
1. Missing DMARC Record:
The most critical error: no DMARC record exists in your DNS. Your domain has zero protection against spoofing. Create a DMARC record starting with p=none to begin monitoring authentication activity.
2. Incorrect Syntax
DMARC records must follow specific formatting rules. Common syntax errors include:
- Missing required tags (v=DMARC1 or p= policy)
- Typos in tag names or values
- Incorrect email format in rua/ruf tags
- Invalid policy values (must be none, quarantine, or reject)
- Missing semicolons between tags
Even small syntax mistakes can cause receiving servers to ignore your entire DMARC record.
3. Policy Set to None
While p=none is appropriate during initial implementation, leaving it indefinitely provides no active protection. Many domains remain in monitoring mode for years, never enforcing authentication policies. After collecting sufficient reports (typically 2-4 weeks), move to p=quarantine or p=reject.
4. SPF/DKIM Misalignment
The most common cause of DMARC failures. Your SPF and DKIM may pass individually, but if the authenticated domains don't align with your "From" domain, DMARC fails. Check that:
- SPF Return-Path domain matches your sending domain
- DKIM signature domain (d=) matches your sending domain
- Alignment mode (relaxed vs strict) is appropriate for your setup
If SPF and DKIM appear to pass but DMARC is still failing due to alignment issues, review our detailed guide on DMARC failing reasons and fixes. It explains common real-world scenarios such as forwarding problems, third-party sender misconfiguration, strict alignment mode errors, and DNS lookup limits — along with step-by-step solutions.
5. Missing rua Tag
Without reporting configured, you can't monitor authentication activity. The rua tag specifies where aggregate reports are sent. Example:
rua=mailto:dmarc@yourdomain.com. These reports are essential for identifying legitimate senders and detecting spoofing attempts.
6. Too Many DNS Lookups
SPF records have a limit of 10 DNS lookups. Exceeding this causes SPF to fail, which can break DMARC authentication. Consolidate your SPF record by:
- Using IP addresses instead of include statements when possible
- Flattening SPF records that include multiple third-party services
- Removing unnecessary entries
7. Subdomain Policy Not Set
The sp= tag defines how subdomains are handled. Without it, subdomains inherit your main domain's policy, which may not be appropriate. Consider setting a specific subdomain policy to prevent subdomains from being exploited while you test the main domain.
8. Percentage Tag Misconfiguration
The pct= tag lets you gradually enforce policies by applying them to only a percentage of emails. Common mistakes include:
- Setting pct=10 and wondering why most spoofed emails still get through
- Forgetting to increase pct= to 100 after testing
- Using pct= with p=none (which has no effect since nothing is blocked anyway)
Use our DMARC checker regularly to identify and fix these issues before they impact your email security or deliverability.
WHY DMARC IS IMPORTANT FOR EMAIL SECURITY
DMARC protects your domain from being exploited for phishing, spam, and email spoofing attacks. Without proper DMARC implementation, cybercriminals can impersonate your domain and send fraudulent emails that appear legitimate to recipients.
1. Prevents Email Spoofing
DMARC works with SPF and DKIM to verify that emails genuinely originate from authorized servers. When an attacker tries to spoof your domain, DMARC checks fail, and the email is blocked or flagged according to your policy.
2. Reduces Phishing Risk
Phishing attacks often rely on spoofed sender addresses to appear trustworthy. DMARC makes it significantly harder for attackers to use your domain in phishing campaigns, protecting both your organization and your customers.
3. Protects Brand Reputation
When attackers spoof your domain for malicious purposes, it damages your brand's credibility. DMARC ensures only verified emails reach recipients, maintaining trust with customers and partners.
4. Improves Email Authentication
Major email providers like Gmail, Microsoft 365, and Yahoo prioritize domains with proper DMARC configuration. Implementing DMARC correctly increases inbox placement rates and reduces the likelihood of legitimate emails being marked as spam.
Regular DMARC checks ensure your email authentication remains properly configured as your infrastructure evolves. Organizations that implement DMARC with enforcement policies (quarantine or reject) report significant reductions in phishing attempts using their domains.
LIMITATIONS OF THIS DMARC CHECKER
Our free DMARC checker provides instant insights into your domain's email authentication configuration. However, like all diagnostic tools, it has certain limitations compared to comprehensive email security solutions.
1. Checks Public DNS Only
This tool queries publicly available DNS records to analyze your DMARC configuration. It cannot access private DNS servers or internal network configurations. The results reflect only what's visible to public mail servers performing authentication.
2. Does Not Modify Records
Our DMARC checker is read-only. It identifies configuration issues but doesn't change your DNS settings. You'll need to manually update your DMARC, SPF, or DKIM records through your DNS provider after identifying problems.
3. Does Not Monitor Ongoing Reports
DMARC checking shows your current configuration, but doesn't collect or analyze the aggregate (rua) and forensic (ruf) reports that receiving servers send. These reports provide critical data about authentication activity, legitimate senders, and potential threats over time.
4. Does Not Aggregate DMARC Reports
DMARC reports arrive in XML format from multiple sources and require specialized tools to parse and analyze effectively. This checker doesn't aggregate, visualize, or track trends in your authentication data across time.
5. No Real-Time Authentication Testing
While the tool verifies your DMARC record configuration, it doesn't actually send test emails to see how receiving servers handle authentication. Real-world email delivery may reveal issues not visible in DNS checking alone.
6. Limited SPF and DKIM Analysis
The checker verifies that SPF and DKIM records exist and checks basic alignment configuration, but it doesn't perform deep validation of SPF include chains, DKIM key strength, or advanced authentication scenarios.